Visible to Intel only — GUID: GUID-AA51A7ED-F61E-48C7-8ED4-12A0E5C44E17
Visible to Intel only — GUID: GUID-AA51A7ED-F61E-48C7-8ED4-12A0E5C44E17
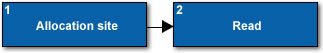
Uninitialized Memory Access
Occurs when a read of an uninitialized memory location is reported.
ID |
Code Location |
Description |
|---|---|---|
1 |
Allocation site |
If present, represents the location and associated call stack from which the memory block containing the offending address was allocated. |
2 |
Read |
Represents the instruction and associated call stack responsible for the uninitialized access. If no allocation is associated with this problem, the memory address might be in uninitialized stack space.
NOTE:
The offset, if shown in the Code Locations pane, represents the byte offset into the allocated buffer where the Uninitialized memory access occurred. |
C Examples
Heap example:
char* pStr = (char*) malloc(20); char c = pStr[0]; // the contents of pStr were not initialized
Stack example (set Analyze stack accesses to Yes when you configure the analysis):
void func()
{
int a;
int b = a * 4; // read of uninitialized variable a
}
Fortran Examples
Heap example:
integer, allocatable :: a(:)
integer :: b
allocate( a(10) )
b = a(1) * 4
Stack example (set Analyze stack accesses to Yes when you configure the analysis):
integer :: a, b
b = a * 4
Possible Correction Strategies
Initialize the offending memory prior to use.